Azure Backup comprehensively protects your data assets in Azure through a simple, secure, and cost-effective solution that requires zero-infrastructure. So backup of Azure VMs placed inside secured networks don't require you to allow access to any IPs or FQDNs. Apart from the data backup platform, you must be careful about data encryption. and IAM roles, Check your results by reviewing the first backup Azure Backup provides you with the Multi-User Authorization (MUA) feature to protect you from such rouge administrator attacks. You may have your own monitoring/ticketing mechanisms to ensure such failures are properly tracked and fixed. ensure the change had the desired impact. Azure Backup requires movement of data from your workload to the Recovery Services vault. So, to distribute the workloads correctly, create four vaults. Access control: Vaults (Recovery Services and Backup vaults) provide the management capabilities and are accessible via the Azure portal, Backup Center, Vault dashboards, SDK, CLI, and even REST APIs. Your business needs may require each department to manage and access their own backups and restores; also, enable them to track their individual usage and cost expense. If you've got a moment, please tell us what we did right so we can do more of it. Also, it shows the backup health through protection level. You can also use NSG tags and Azure Firewall tags for allowing access to Azure AD, as applicable. contain one and only one backup plan to simplify debugging and troubleshooting. Not allowing proper connectivity to the required Azure services may lead to failure in operations like database discovery, configuring backup, performing backups, and restoring data. You won't be able to restore the VM nor use Resume backup option. An example of a data backed up according to the 3-2-1 Rule would be a main server in a businesss headquarters, a cloud backup, and a backup NAS drive. Most data backup plans include backup for individual devices. Apart from having a clear roadmap to navigate through the Cloud Adoption Journey, you must plan your cloud deployment's subscription design and account structure to match your organization's ownership, billing, and management capabilities. Ensure that the change you made had the intended impact on the effective policy. levels are complete by themselves. Thanks for letting us know this page needs work. This field is for validation purposes and should be left unchanged. Please refer to your browser's Help pages for instructions. The guidance covered in this article can make it easier to design your backup solution on Azure using established patterns and avoid known pitfalls. If you only need to retain your events for 90 days or less, you don't need to set up archives to a storage account, since Activity Log events are kept in the Azure platform for 90 days. To help you optimize your storage costs, Azure Backup provides you with Archive Tier, which is an access tier especially designed for Long-Term Retention (LTR) of the backup data. Azure Backup provides an in-built alert notification mechanism via e-mail for failures, warnings, and critical operations. Using its advanced file filter feature, users can easily find and mark files. If you're retiring or decommissioning your data source (VM, application), but need to retain data for audit or compliance purposes, then you can use this option to stop all future backup jobs from protecting your data source and retain the recovery points that have been backed up. If there is any budget constrain, companies should consider backups on an external drive and a cloud platform. You have to consider the endpoints such as desktops, laptops, tablets, and phones your employees and colleagues use to perform their duties. using GetEffectivePolicy, Store copies of your backups in other AWS Regions and accounts in your organization, Use stack sets to create the required backup vaults Backing up multiple systems typically involves more complexity. To maximize the effectiveness of disaster recovery (DR) efforts, the backup policy should also clearly outline areas of responsibility for an organizations approach to backup. Azure Backup supports backup and restore of Azure VMs that have their OS/data disks encrypted with Azure Disk Encryption (ADE). Whether there is a system crash, natural disaster, or cyberattacknothing can stop you when you have backup data. This can be useful for taking backups that dont fit your scheduled backup or for taking granular backup (for example, multiple IaaS VM backups per day since scheduled backup permits only one backup per day). As your organizational footprint grows, you might want to move workloads across subscriptions for the following reasons: align by backup policy, consolidate vaults, trade-off on lower redundancy to save on cost (move from GRS to LRS). It means making 3 copies of data and storing the backup copies on 2 different devices/platforms, one of which should be offsite storage. representative accounts below the level where you made the change. created in each account, child control inheritance This helps you to separate access boundaries for the users by allowing you to grant access (using Azure role-based access control Azure RBAC) to the relevant stakeholders. If you need to retain this data, then you can export as an Excel file and retain them. Learn more here. specify the ARN of the backup vault in which to store the copy of the backup. Storing such huge data in a Standard Tier is costly and isnt economical. For example, its better to schedule the daily automated backup during night, around 2-3 AM, rather than scheduling it in the day time when the usage of the resources high. The in-built alerts can't be customized and are restricted to emails defined in the Azure portal. identify the account by using the $account variable when you You can also get notifications through built-in Recovery Services vault activity logs. It might say, for instance, that the policy is intended to standardize backup procedures across the organization. Utilizing remote storage is just one component in the 3-2-1 Rule. Storage Replication type by default is set to Geo-redundant (GRS). It reduces the time needed to transform and copy data back from the vault. After you make a change to a backup policy, check the effective policies for the way you intended. Moreover, there will be no issue when the business needs to recover it. Once you schedule backup at your preferred time, the software will run automatically and make backup copies. Multi-user authorization helps protect against a rogue administrator performing destructive operations (that is, disabling soft-delete), by ensuring that every privileged/destructive operation is done only after getting approval from a security administrator. The document could set down procedures, responsible parties, and specify related documentation (well review the contents of the typical backup policy later in the article).
Main Office: This will offer you a great advantage if your central server gets compromised in any way. Stop protection and delete backup data. enables you to run your backup plans with assurance that the dependencies are already This option drastically reduces the time to recover your data to the original storage.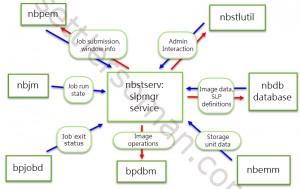 Policy management: Azure Backup Policies within each vault define when the backups should be triggered and the duration they need to be retained. met. You can't selectively delete specific recovery points. Also, a malicious actor may delete your production backup items. The following diagram explains about how different Azure built-in roles work: In the above diagram, User2 and User3 are Backup Readers. To fulfill all these needs, use Azure Private Endpoint, which is a network interface that connects you privately and securely to a service powered by Azure Private Link. Think of it as the definitive word as to which backup practices will be followed. Before finalizing your vault design, review the vault support matrixes to understand the factors that might influence or limit your design choices. Azure Backup Policy has two components: Schedule (when to take backup) and Retention (how long to retain backup). hbspt.cta.load(5442029, 'a99bf554-4786-40d2-8e73-43bf625d6417', {}); Further reading Building a Cloud Disaster Recovery Plan: Tips and Approaches. Use it to identify resources that aren't configured for backup, and ensure that you don't ever miss protecting critical data in your growing estate. Automated storage management: Azure Backup automates provisioning and managing storage accounts for the backup data to ensure it scales as the backup data grows. 919-781-8885, Copier Service and Supplies: While its easy to start protecting infrastructure and applications on Azure, when you ensure that the underlying Azure resources are set up correctly and being used optimally you can accelerate your time to value. Review the trade-offs between lower costs and higher data durability and choose the best option for your scenario. 919-781-0222, Copyright 2022 Copy CEI. If you do not back up the data of these devices, you might lose them forever in case the devices get lost or stolen. As we head into a new decade, data backup is more important than ever. Monitoring Policy: To generate the Backup Reports for your resources, enable the diagnostic settings when you create a new vault. You can send data to an Azure Storage account if you want to retain your log data longer than 90 days for audit, static analysis, or backup. Secure encrypted backups: Azure Backup ensures your backup data is stored in a secure manner, leveraging built-in security capabilities of the Azure platform, such as Azure role-based access control (Azure RBAC) and Encryption. Managing backup and DR in the enterprise environment is a complex process and the person entrusted to lead it is responsible for maintaining the integrity of data across multiple business systems. Users can also choose from full, scheduled, incremental, and differential backups to cover every bit of data. It encrypts your file in transit and in storage to ensure maximum security. Submit Your General Questions And Comments Through This Form. Watch the following video to learn how to leverage Azure Monitor to configure various notification mechanisms for critical alerts. You Once you configure the backup, the option to modify is disabled. Hybrid workloads (DPM/MABS) can also send data to LA and use LA to provide common alerts across workloads supported by Azure Backup. This is called Instant Restore. Malicious delete protection: Protect against any accidental and malicious attempts for deleting your backups via soft delete of backups. Even with the most advanced protection against hacking, your business can become a victim of hacking and ransomware attacks. Call us at 919-781-8885 or fill out the contact form below to get started! It helps protect your mission critical workloads running in the cloud, and ensures your backups are always available and managed at scale across your entire backup estate. Else, you can also perform backups manually if you own a small or medium business. Use Archive Tier for Long-Term Retention (LTR) and save costs: Consider the scenario where youve older backup data that you rarely access, but is required to be stored for a long period (for example, 99 years) for compliance reasons. However, the use of Azure Key Vault, where your key is stored, incur costs, which are a reasonable expense in return for the higher data security. Usually, backup solution providers offer different retention schedules for various types of backup up data. The following are the best practices. If you need to retain and view the operational activities for long-term, then use Reports. Azure Backup enables data protection for various workloads (on-premises and cloud).
Policy management: Azure Backup Policies within each vault define when the backups should be triggered and the duration they need to be retained. met. You can't selectively delete specific recovery points. Also, a malicious actor may delete your production backup items. The following diagram explains about how different Azure built-in roles work: In the above diagram, User2 and User3 are Backup Readers. To fulfill all these needs, use Azure Private Endpoint, which is a network interface that connects you privately and securely to a service powered by Azure Private Link. Think of it as the definitive word as to which backup practices will be followed. Before finalizing your vault design, review the vault support matrixes to understand the factors that might influence or limit your design choices. Azure Backup Policy has two components: Schedule (when to take backup) and Retention (how long to retain backup). hbspt.cta.load(5442029, 'a99bf554-4786-40d2-8e73-43bf625d6417', {}); Further reading Building a Cloud Disaster Recovery Plan: Tips and Approaches. Use it to identify resources that aren't configured for backup, and ensure that you don't ever miss protecting critical data in your growing estate. Automated storage management: Azure Backup automates provisioning and managing storage accounts for the backup data to ensure it scales as the backup data grows. 919-781-8885, Copier Service and Supplies: While its easy to start protecting infrastructure and applications on Azure, when you ensure that the underlying Azure resources are set up correctly and being used optimally you can accelerate your time to value. Review the trade-offs between lower costs and higher data durability and choose the best option for your scenario. 919-781-0222, Copyright 2022 Copy CEI. If you do not back up the data of these devices, you might lose them forever in case the devices get lost or stolen. As we head into a new decade, data backup is more important than ever. Monitoring Policy: To generate the Backup Reports for your resources, enable the diagnostic settings when you create a new vault. You can send data to an Azure Storage account if you want to retain your log data longer than 90 days for audit, static analysis, or backup. Secure encrypted backups: Azure Backup ensures your backup data is stored in a secure manner, leveraging built-in security capabilities of the Azure platform, such as Azure role-based access control (Azure RBAC) and Encryption. Managing backup and DR in the enterprise environment is a complex process and the person entrusted to lead it is responsible for maintaining the integrity of data across multiple business systems. Users can also choose from full, scheduled, incremental, and differential backups to cover every bit of data. It encrypts your file in transit and in storage to ensure maximum security. Submit Your General Questions And Comments Through This Form. Watch the following video to learn how to leverage Azure Monitor to configure various notification mechanisms for critical alerts. You Once you configure the backup, the option to modify is disabled. Hybrid workloads (DPM/MABS) can also send data to LA and use LA to provide common alerts across workloads supported by Azure Backup. This is called Instant Restore. Malicious delete protection: Protect against any accidental and malicious attempts for deleting your backups via soft delete of backups. Even with the most advanced protection against hacking, your business can become a victim of hacking and ransomware attacks. Call us at 919-781-8885 or fill out the contact form below to get started! It helps protect your mission critical workloads running in the cloud, and ensures your backups are always available and managed at scale across your entire backup estate. Else, you can also perform backups manually if you own a small or medium business. Use Archive Tier for Long-Term Retention (LTR) and save costs: Consider the scenario where youve older backup data that you rarely access, but is required to be stored for a long period (for example, 99 years) for compliance reasons. However, the use of Azure Key Vault, where your key is stored, incur costs, which are a reasonable expense in return for the higher data security. Usually, backup solution providers offer different retention schedules for various types of backup up data. The following are the best practices. If you need to retain and view the operational activities for long-term, then use Reports. Azure Backup enables data protection for various workloads (on-premises and cloud).
To ensure continuity and operational efficiency, a central backup policy should be documented and periodically revised. organization. As a backup user or administrator, you should be able to monitor all backup solutions and get notified on important scenarios. using the child control inheritance Effective vault design helps organizations establish a structure to organize and manage the backup assets in Azure to support your business priorities. With soft-delete, if a user deletes the backup (of a VM, SQL Server database, Azure file share, SAP HANA database), the backup data is retained for 14 additional days, allowing the recovery of that backup item with no data loss. Does Your Business Need a Network & Security Assessment? Consider the following security guidelines for your Azure Backup solution: Azure role-based access control (Azure RBAC) enables fine-grained access management, segregation of duties within your team and granting only the amount of access to users necessary to perform their jobs. Data backup also serves archival purposes. We may earn affiliate commissions from buying links on this site. To distribute the backup traffic, we recommend you back up different VMs at different times of the day.
Unplanned (on-demand requirement) - if you don't know in advance, then use you can use on-demand with specific custom retention settings (these custom retention settings aren't impacted by policy settings).
If you are tasked with creating a backup policy, but you clearly understand that its not a formal document, you should better ask about the exact nature of the needed document. Learn more about how to create and use private endpoints for Azure Backup inside your virtual networks. As an official corporate document, the backup policy will tend to follow a tried and tested formula. Policies that contain multiple plans are more complicated to troubleshoot because of You can have a duplicate copy of your data anywhere for backup purposes. Backup center allows you to have a single pane to manage all Backup tasks. Use the copy_actions section of the policy to specify a Ensure if you need to enforce security standards and separate access boundaries. Also, the following tools such as Azure Price Calculator and Azure Advisor play an important role in the cost management process. Learn more. When you do so, you can expect the following: Azure Backup provides you the flexibility to stop protecting and manage your backups: Stop protection and retain backup data. As you are familiar with the importance of data backup, it is time to learn data backup best practices. Learn how we can secure your data by scheduling your consultation. You can achieve this by retrieving relevant backup data via Azure Resource Graph (ARG) and combine it with corrective PowerShell/CLI procedure. Learn more. It's Azure's built-in data protection solution for a wide range of workloads. Following are some of the questions you should ask yourself while formulating a perfect backup strategy. While protecting your critical data with Azure Backup, you wouldnt want your resources to be accessible from the public internet. The backup policy might spell out exactly which employees (or departments) and assets fall under the governance of this backup policy. The backup data gets stored in its dedicated data centers with biometric security, 24/7 staff, and power backup. The easiest way to solve this problem is to not allow work to be done on personal devices. vault in one or more accounts in your organization, separate from the account in Learn more about Azure Backup Instant Recovery capability. Follow these steps to review and modify the settings. Consider the following guidelines: Use the pricing calculator to evaluate and optimize cost by adjusting various levers. Zone redundant storage (ZRS) is a good storage option for a high Data Durability along with Data Residency. You might want to store it in an external data storage device like an external HDD, SSD, and USB.
How would you protect your data if your administrator goes rogue and compromises your system? To get started with Azure Backup, plan your backup needs. You can specify individual email addresses or distribution lists to be notified when an alert is generated. Soft delete by default is Enabled on newly created vaults to protect backup data from accidental or malicious deletes. A formal backup policy is very useful in these cases to set down standards for the workflows of many delegated backup administrators.
operators, view the effective policy by using
carefully considering the change's impact on all accounts below that level. This can be achieved by using private endpoints or by allowing access to the required public IP addresses or FQDNs. You can use it to backup only selected items instead of all disk objects. At the same time, there is no restriction in terms of file size or file count on this platform. unexpected result does happen. A disaster recovery plan is essential, especially if you live in a natural disaster-prone area. EaseUS Todo Backup protects your data with disk imaging technology. Azure Backup provides built-in job monitoring for operations such as configuring backup, back up, restore, delete backup, and so on. The access is only allowed through Azure Backup management operations, such as restore. If your organization is large enough to be authoring a backup policy, then the backup policy should also probably clearly delineate its scope. One of the requirements of Azure Backup is that the vaults are required to be present in the same region as the resource to be backed-up. Learn more. For more information, see Create a Stack Set with Self-Managed Permissions in the AWS CloudFormation User Guide. This feature keeps those resources in compliance with your corporate standards. This is also useful when you have multiple backup solutions. A rogue admin can delete all your business-critical data or even turn off all the security measures that may leave your system vulnerable to cyber-attacks.
You can define the policy based on the type of data that's being backed up, RTO/RPO requirements, operational or regulatory compliance needs and workload type (for example, VM, database, files). The user interface of this utility is available in all major languages, including English, French, German, Japanese, and Spanish. You can also tier your data from operational storage to vault storage. However, there are circumstances in which authoring this kind of document is essential. Instead, have each policy Learn more here. backup vaults and AWS Identity and Access Management (IAM) roles in each of the member accounts in your To simplify debugging, start with simple policies and make changes one item at a time. Data has turned out to be the most crucial aspect of a business.


Main Office: This will offer you a great advantage if your central server gets compromised in any way. Stop protection and delete backup data. enables you to run your backup plans with assurance that the dependencies are already This option drastically reduces the time to recover your data to the original storage.
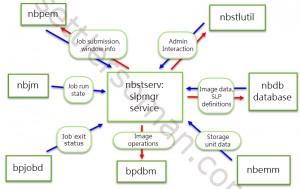 Policy management: Azure Backup Policies within each vault define when the backups should be triggered and the duration they need to be retained. met. You can't selectively delete specific recovery points. Also, a malicious actor may delete your production backup items. The following diagram explains about how different Azure built-in roles work: In the above diagram, User2 and User3 are Backup Readers. To fulfill all these needs, use Azure Private Endpoint, which is a network interface that connects you privately and securely to a service powered by Azure Private Link. Think of it as the definitive word as to which backup practices will be followed. Before finalizing your vault design, review the vault support matrixes to understand the factors that might influence or limit your design choices. Azure Backup Policy has two components: Schedule (when to take backup) and Retention (how long to retain backup). hbspt.cta.load(5442029, 'a99bf554-4786-40d2-8e73-43bf625d6417', {}); Further reading Building a Cloud Disaster Recovery Plan: Tips and Approaches. Use it to identify resources that aren't configured for backup, and ensure that you don't ever miss protecting critical data in your growing estate. Automated storage management: Azure Backup automates provisioning and managing storage accounts for the backup data to ensure it scales as the backup data grows. 919-781-8885, Copier Service and Supplies: While its easy to start protecting infrastructure and applications on Azure, when you ensure that the underlying Azure resources are set up correctly and being used optimally you can accelerate your time to value. Review the trade-offs between lower costs and higher data durability and choose the best option for your scenario. 919-781-0222, Copyright 2022 Copy CEI. If you do not back up the data of these devices, you might lose them forever in case the devices get lost or stolen. As we head into a new decade, data backup is more important than ever. Monitoring Policy: To generate the Backup Reports for your resources, enable the diagnostic settings when you create a new vault. You can send data to an Azure Storage account if you want to retain your log data longer than 90 days for audit, static analysis, or backup. Secure encrypted backups: Azure Backup ensures your backup data is stored in a secure manner, leveraging built-in security capabilities of the Azure platform, such as Azure role-based access control (Azure RBAC) and Encryption. Managing backup and DR in the enterprise environment is a complex process and the person entrusted to lead it is responsible for maintaining the integrity of data across multiple business systems. Users can also choose from full, scheduled, incremental, and differential backups to cover every bit of data. It encrypts your file in transit and in storage to ensure maximum security. Submit Your General Questions And Comments Through This Form. Watch the following video to learn how to leverage Azure Monitor to configure various notification mechanisms for critical alerts. You Once you configure the backup, the option to modify is disabled. Hybrid workloads (DPM/MABS) can also send data to LA and use LA to provide common alerts across workloads supported by Azure Backup. This is called Instant Restore. Malicious delete protection: Protect against any accidental and malicious attempts for deleting your backups via soft delete of backups. Even with the most advanced protection against hacking, your business can become a victim of hacking and ransomware attacks. Call us at 919-781-8885 or fill out the contact form below to get started! It helps protect your mission critical workloads running in the cloud, and ensures your backups are always available and managed at scale across your entire backup estate. Else, you can also perform backups manually if you own a small or medium business. Use Archive Tier for Long-Term Retention (LTR) and save costs: Consider the scenario where youve older backup data that you rarely access, but is required to be stored for a long period (for example, 99 years) for compliance reasons. However, the use of Azure Key Vault, where your key is stored, incur costs, which are a reasonable expense in return for the higher data security. Usually, backup solution providers offer different retention schedules for various types of backup up data. The following are the best practices. If you need to retain and view the operational activities for long-term, then use Reports. Azure Backup enables data protection for various workloads (on-premises and cloud).
Policy management: Azure Backup Policies within each vault define when the backups should be triggered and the duration they need to be retained. met. You can't selectively delete specific recovery points. Also, a malicious actor may delete your production backup items. The following diagram explains about how different Azure built-in roles work: In the above diagram, User2 and User3 are Backup Readers. To fulfill all these needs, use Azure Private Endpoint, which is a network interface that connects you privately and securely to a service powered by Azure Private Link. Think of it as the definitive word as to which backup practices will be followed. Before finalizing your vault design, review the vault support matrixes to understand the factors that might influence or limit your design choices. Azure Backup Policy has two components: Schedule (when to take backup) and Retention (how long to retain backup). hbspt.cta.load(5442029, 'a99bf554-4786-40d2-8e73-43bf625d6417', {}); Further reading Building a Cloud Disaster Recovery Plan: Tips and Approaches. Use it to identify resources that aren't configured for backup, and ensure that you don't ever miss protecting critical data in your growing estate. Automated storage management: Azure Backup automates provisioning and managing storage accounts for the backup data to ensure it scales as the backup data grows. 919-781-8885, Copier Service and Supplies: While its easy to start protecting infrastructure and applications on Azure, when you ensure that the underlying Azure resources are set up correctly and being used optimally you can accelerate your time to value. Review the trade-offs between lower costs and higher data durability and choose the best option for your scenario. 919-781-0222, Copyright 2022 Copy CEI. If you do not back up the data of these devices, you might lose them forever in case the devices get lost or stolen. As we head into a new decade, data backup is more important than ever. Monitoring Policy: To generate the Backup Reports for your resources, enable the diagnostic settings when you create a new vault. You can send data to an Azure Storage account if you want to retain your log data longer than 90 days for audit, static analysis, or backup. Secure encrypted backups: Azure Backup ensures your backup data is stored in a secure manner, leveraging built-in security capabilities of the Azure platform, such as Azure role-based access control (Azure RBAC) and Encryption. Managing backup and DR in the enterprise environment is a complex process and the person entrusted to lead it is responsible for maintaining the integrity of data across multiple business systems. Users can also choose from full, scheduled, incremental, and differential backups to cover every bit of data. It encrypts your file in transit and in storage to ensure maximum security. Submit Your General Questions And Comments Through This Form. Watch the following video to learn how to leverage Azure Monitor to configure various notification mechanisms for critical alerts. You Once you configure the backup, the option to modify is disabled. Hybrid workloads (DPM/MABS) can also send data to LA and use LA to provide common alerts across workloads supported by Azure Backup. This is called Instant Restore. Malicious delete protection: Protect against any accidental and malicious attempts for deleting your backups via soft delete of backups. Even with the most advanced protection against hacking, your business can become a victim of hacking and ransomware attacks. Call us at 919-781-8885 or fill out the contact form below to get started! It helps protect your mission critical workloads running in the cloud, and ensures your backups are always available and managed at scale across your entire backup estate. Else, you can also perform backups manually if you own a small or medium business. Use Archive Tier for Long-Term Retention (LTR) and save costs: Consider the scenario where youve older backup data that you rarely access, but is required to be stored for a long period (for example, 99 years) for compliance reasons. However, the use of Azure Key Vault, where your key is stored, incur costs, which are a reasonable expense in return for the higher data security. Usually, backup solution providers offer different retention schedules for various types of backup up data. The following are the best practices. If you need to retain and view the operational activities for long-term, then use Reports. Azure Backup enables data protection for various workloads (on-premises and cloud). To ensure continuity and operational efficiency, a central backup policy should be documented and periodically revised. organization. As a backup user or administrator, you should be able to monitor all backup solutions and get notified on important scenarios. using the child control inheritance Effective vault design helps organizations establish a structure to organize and manage the backup assets in Azure to support your business priorities. With soft-delete, if a user deletes the backup (of a VM, SQL Server database, Azure file share, SAP HANA database), the backup data is retained for 14 additional days, allowing the recovery of that backup item with no data loss. Does Your Business Need a Network & Security Assessment? Consider the following security guidelines for your Azure Backup solution: Azure role-based access control (Azure RBAC) enables fine-grained access management, segregation of duties within your team and granting only the amount of access to users necessary to perform their jobs. Data backup also serves archival purposes. We may earn affiliate commissions from buying links on this site. To distribute the backup traffic, we recommend you back up different VMs at different times of the day.
Unplanned (on-demand requirement) - if you don't know in advance, then use you can use on-demand with specific custom retention settings (these custom retention settings aren't impacted by policy settings).
If you are tasked with creating a backup policy, but you clearly understand that its not a formal document, you should better ask about the exact nature of the needed document. Learn more about how to create and use private endpoints for Azure Backup inside your virtual networks. As an official corporate document, the backup policy will tend to follow a tried and tested formula. Policies that contain multiple plans are more complicated to troubleshoot because of You can have a duplicate copy of your data anywhere for backup purposes. Backup center allows you to have a single pane to manage all Backup tasks. Use the copy_actions section of the policy to specify a Ensure if you need to enforce security standards and separate access boundaries. Also, the following tools such as Azure Price Calculator and Azure Advisor play an important role in the cost management process. Learn more. When you do so, you can expect the following: Azure Backup provides you the flexibility to stop protecting and manage your backups: Stop protection and retain backup data. As you are familiar with the importance of data backup, it is time to learn data backup best practices. Learn how we can secure your data by scheduling your consultation. You can achieve this by retrieving relevant backup data via Azure Resource Graph (ARG) and combine it with corrective PowerShell/CLI procedure. Learn more. It's Azure's built-in data protection solution for a wide range of workloads. Following are some of the questions you should ask yourself while formulating a perfect backup strategy. While protecting your critical data with Azure Backup, you wouldnt want your resources to be accessible from the public internet. The backup policy might spell out exactly which employees (or departments) and assets fall under the governance of this backup policy. The backup data gets stored in its dedicated data centers with biometric security, 24/7 staff, and power backup. The easiest way to solve this problem is to not allow work to be done on personal devices. vault in one or more accounts in your organization, separate from the account in Learn more about Azure Backup Instant Recovery capability. Follow these steps to review and modify the settings. Consider the following guidelines: Use the pricing calculator to evaluate and optimize cost by adjusting various levers. Zone redundant storage (ZRS) is a good storage option for a high Data Durability along with Data Residency. You might want to store it in an external data storage device like an external HDD, SSD, and USB.
How would you protect your data if your administrator goes rogue and compromises your system? To get started with Azure Backup, plan your backup needs. You can specify individual email addresses or distribution lists to be notified when an alert is generated. Soft delete by default is Enabled on newly created vaults to protect backup data from accidental or malicious deletes. A formal backup policy is very useful in these cases to set down standards for the workflows of many delegated backup administrators.
operators, view the effective policy by using
carefully considering the change's impact on all accounts below that level. This can be achieved by using private endpoints or by allowing access to the required public IP addresses or FQDNs. You can use it to backup only selected items instead of all disk objects. At the same time, there is no restriction in terms of file size or file count on this platform. unexpected result does happen. A disaster recovery plan is essential, especially if you live in a natural disaster-prone area. EaseUS Todo Backup protects your data with disk imaging technology. Azure Backup provides built-in job monitoring for operations such as configuring backup, back up, restore, delete backup, and so on. The access is only allowed through Azure Backup management operations, such as restore. If your organization is large enough to be authoring a backup policy, then the backup policy should also probably clearly delineate its scope. One of the requirements of Azure Backup is that the vaults are required to be present in the same region as the resource to be backed-up. Learn more. For more information, see Create a Stack Set with Self-Managed Permissions in the AWS CloudFormation User Guide. This feature keeps those resources in compliance with your corporate standards. This is also useful when you have multiple backup solutions. A rogue admin can delete all your business-critical data or even turn off all the security measures that may leave your system vulnerable to cyber-attacks.
You can define the policy based on the type of data that's being backed up, RTO/RPO requirements, operational or regulatory compliance needs and workload type (for example, VM, database, files). The user interface of this utility is available in all major languages, including English, French, German, Japanese, and Spanish. You can also tier your data from operational storage to vault storage. However, there are circumstances in which authoring this kind of document is essential. Instead, have each policy Learn more here. backup vaults and AWS Identity and Access Management (IAM) roles in each of the member accounts in your To simplify debugging, start with simple policies and make changes one item at a time. Data has turned out to be the most crucial aspect of a business.

